Exploiting Security Vulnerabilities
Professor Xinyu Xing and his current and former students recently participated in three flagship security summits
The Northwestern Security and Privacy Group considerably expanded work in software and system security, network security, artificial intelligence (AI) security, cryptography, and data privacy with the recent appointments of four faculty members — Sruti Bhagavatula, assistant professor of instruction; V.S. Subrahmanian, Walter P. Murphy Professor of Computer Science in Northwestern Engineering and a faculty fellow at the Northwestern Roberta Buffett Institute for Global Affairs; Xiao Wang, assistant professor of computer science; and Xinyu Xing, associate professor of computer science at Northwestern Engineering.
 Xing, whose research focus includes kernel security, reverse engineering, and AI security, recently participated in three flagship security summits with his current and former students: Pwn2Own, DEF CON, and BlackHat.
Xing, whose research focus includes kernel security, reverse engineering, and AI security, recently participated in three flagship security summits with his current and former students: Pwn2Own, DEF CON, and BlackHat.
Pwn2Own
The 2022 Pwn2Own security contest in Vancouver, run by Trend Micro’s Zero Day Initiative and hosted by the CanSecWest Conference, rewards teams with for successful exploits of unique zero-day vulnerabilities – flaws in a system or device discovered by hackers and not yet patched by the vendor. The international competition invites hackers to compete to find defects in products including Apple Safari, Microsoft Windows and Teams, Mozilla Firefox, Oracle VirtualBox, and Tesla.
“Team Tutelary” – composed of Xing; Zhenpeng Lin, a fourth-year PhD student in computer science at the McCormick School of Engineering advised by Xing; and Yueqi Chen, assistant professor in computer science at the University of Colorado Boulder and former visiting scholar in Northwestern CS advised by Xing – successfully demonstrated a use-after-free bug leading to elevation of privilege on the open-source desktop operating system Ubuntu Desktop. Use-after-free bugs are security vulnerabilities that can cause unauthorized access to a target system.
Ubuntu Desktop runs the Linux kernel, which is the core interface between a system’s hardware and software. Xing’s research group focuses on the security of the Linux kernel, so they targeted the widely used Ubuntu Desktop to demonstrate their newly developed exploitation technique.
“The demonstration of the use-after-free bug against this system makes the Linux community aware of the threat,” Lin said. “The Linux kernel developer can now take immediate action to fix their system.”
Pwn2Own competitors have a maximum of three exploit attempts. Team Tutelary succeeded on their first attempt and earned a prize of $40,000 and four points toward the “Master of Pwn” – the title given for the overall winner of the contest.
DEFCON CTF
The Capture the Flag (CTF) team supervised by Xing called “Straw Hat” competed in DEF CON 30 CTF in Las Vegas this summer after finishing in eighth place in the qualifying round. Team members included Lin, visiting pre-doctoral fellow Qi Qin, first-year PhD students Yuhang Wu and Zheng Yu, research intern Pedro Guerra, and research associate Qi Su. Straw Hat is a joint team, which also includes Super Rookie, Nu1L, and W&M.
CTF competitions involve breaking into intentionally vulnerable programs or websites, locating hidden “flags,” and stealing flags from fellow competitors.
The Straw Hat team placed seventh in the 72-hour CTF hacking contest.
“Competitions like DEF CON CTF help students gain security knowledge and obtain hands-on skills to perform blue/red team work in the future,” Xing said.
Red teams operate offensively, attacking systems and breaking into defenses. Blue teams are defensive and are responsible for maintaining defenses against security threats.
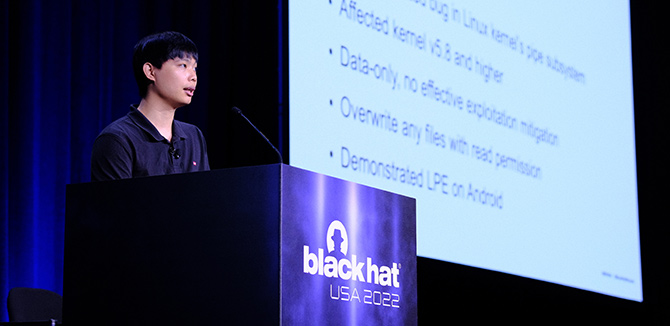
Black Hat USA
At Black Hat USA, also held Las Vegas, Lin, Wu, and Xing presented the briefing “Cautious: A New Exploitation Method! No Pipe but as Nasty as Dirty Pipe,” detailing an exploitation technique named "DirtyCred" and demonstrating the techniques on the Android system and containers.
Lin noted that DirtyCred can achieve the same effect as Dirty Pipe, and is even more powerful. Unlike Dirty Pipe, DirtyCred can achieve privilege escalation on containers. The technique is also capable of empowering different vulnerabilities.
“To the best of our knowledge, our exploitation is the first general method that helps develop a universal exploit to different versions of kernel and different architectures,” Xing said. “It greatly unloads the burden of exploit migration across versions and architectures. Since our exploitation is general and powerful, it also imposes a great challenge to the existing kernel defense architecture.”
After the Black Hat summit, the team further demonstrated the DirtyCred technique with an eight-year-old kernel vulnerability.